What is Phishing Attack in Cyber Security - Complete Guide
4.8 (619) · $ 19.50 · In stock
What Is A Whaling Phishing Attack? - Cisco
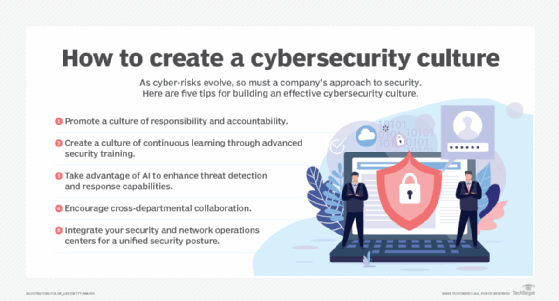
The Ultimate Guide to Cybersecurity Planning for Businesses
[Hermans, Kris] on . *FREE* shipping on qualifying offers. Mastering Phishing: A Comprehensive Guide To Become An Expert In Phishing

Mastering Phishing: A Comprehensive Guide To Become An Expert In Phishing

What is Phishing Attack in Cyber Security - Complete Guide
What is the Goal Behind Phishing Emails?

Phishing - Wikipedia
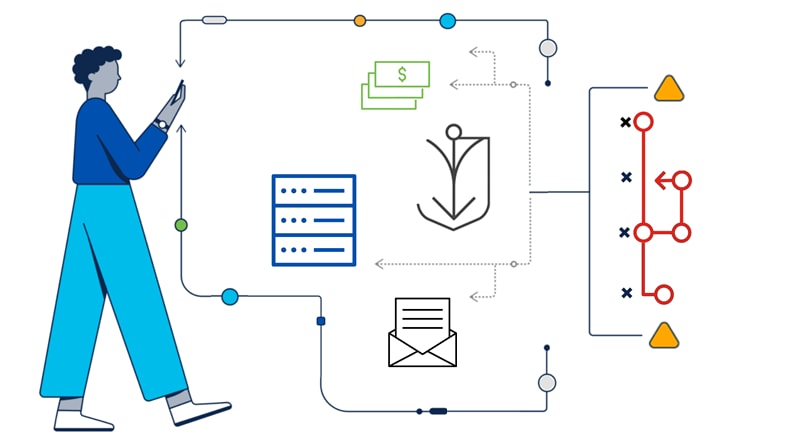
7 Cyber Attack Vectors & How to Protect Them

Phishing Analysis Fundamentals TryHackMe Full Walkthrough

Best Cybersecurity Courses: Beginners, Advanced & Specializations

What are Indicators of Attack (IOAs)? How they Differ from IOCs



?$M-305-305-D$&fit=crop&fmt=jpg)



